Beginner’s Guide to Blockchain
By Sidharth Malhotra
Part 1 – A Simple Guide to Understand Blockchain with a Real-World Analogy
Everyone is talking about Bitcoin these days, from your barber to your friends working the stock market. Don’t worry. This article is not about making money from Bitcoin. However, I will try to help you understand the underlying technology which makes Bitcoin work and how this concept of blockchain can be useful in the coming decades.
Historical Overview
October 31, 2008, a white paper from an anonymous person or organization named Satoshi Nakamoto was published which explained a novel approach to send money from sender to receiver directly without involving any financial intermediaries. The paper gave a name to this concept — Bitcoin. Since, Bitcoin uses some underlying concepts of cryptography, this new way of exchanging money was categorized as cryptocurrency. The only purpose of Bitcoin was for financial transactions, but researchers realized that its foundational technology can be harvested to build other secure and robust applications that can revolutionize the way current systems work. “Blockchain” was the name given to this foundational technology. Lots of technical words? Let’s simplify!
What is Blockchain? — A Real World Parking Analogy
Centralized Parking Scenario
Let’s imagine that you live in a city, which has space to accommodate 200 cars at one time (assume that there is one parking structure with a ground floor). This facility has a main gate which stays locked and is only opened when a car moves in or out. Now let’s analyze this single parking building from different points of view.
Price: Since some private company built this parking facility exclusively for parking purposes and all the maintenance and operating costs will be borne by the owner company, there will be a high fee for renting out a single parking space.
Security: If thieves get access to the main door, they can easily get to your car (take its contents, wheels, or fuel, or damage the vehicle, etc.)
Limit: What if the number of cars in your city grows by 50 percent? The parking structure will not have enough space for all cars and so another private agency builds a new parking facility.
Trusted: You trust the parking operator, who is responsible for taking care of security, maintenance and reliability.
Centralized: Since all the cars are in one location, we can consider it to be centralized parking.
Decentralized Parking Scenario
Now, let’s modify the current scenario. Imagine that there are 200 houses in your city and each house has a two-car garage. However, to simplify the explanation, let’s assume each house just has one car (the same number of cars that fill the parking facility described above). Each house would have one empty space out of the two available. Now, let’s say people decide to rent out the extra space to anyone who needs parking. This model would solve the problem of parking 200 cars or more without the need of building another central parking facility for the entire city. Similar to the previous scenario, let’s analyze
this one:
Price: Since the second parking space wasn’t built exclusively for renting purposes and the cost of maintenance will be little, the cost to rent that extra space will be low comparatively to the big central parking space
Security: Since each car is secured in a different location, thieves will have less opportunity to access to the cars, thus providing a more secure environment. (Security in blockchain is a bit different but for simplicity let’s consider it this way for now!)
Limit: As the number of houses increase, assuming each new house also has an extra parking space, the space to park more cars will keep increasing, thus increasing the network of lessee and lessor.
Trustless: Since no central authority controls these distributed parking spaces, we assume that there will be certain rules set by all the participating home owners for renting out their spaces.
Decentralized: As mentioned in the previous point, these parking spaces are distributed throughout the city, so we can consider it to be a decentralized parking.
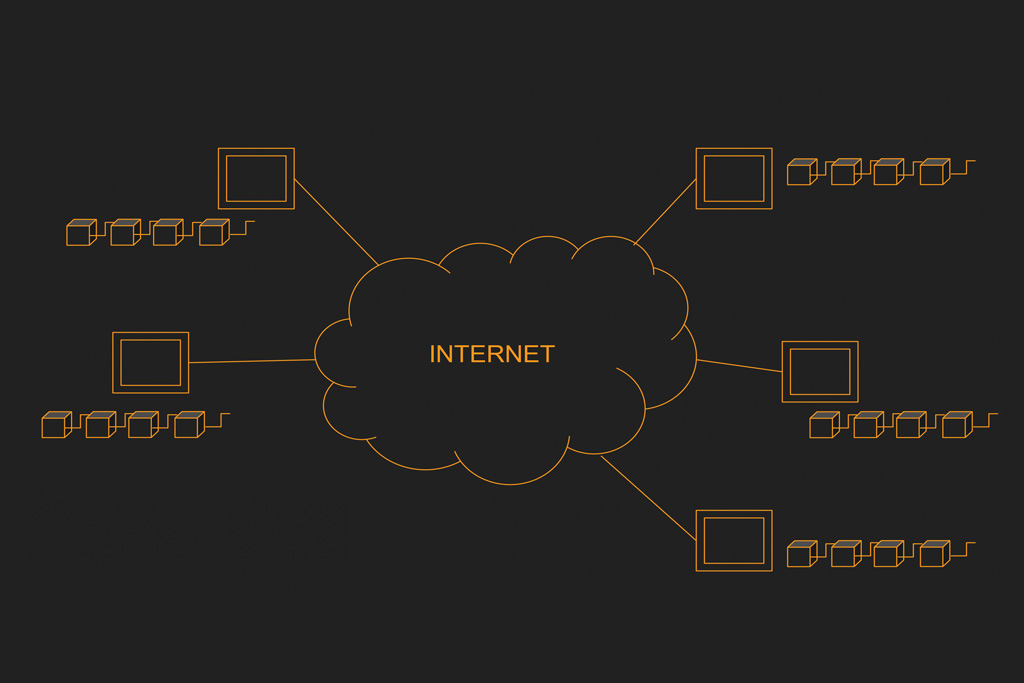
Parking Model to Technical Model
The above analogy provides the foundation for understanding the actual technical infrastructure of the Blockchain. The parking model presents a very basic overview of Blockchain in some real-world language. Now, let’s try to match the components of our parking example to the actual technical model.
The city parking facility is a centralized system like AWS, Google Cloud etc. (These cloud platforms are also distributed at some level but for the sake of simplicity, we will assume them to be a single entity.)
The cars are the data and applications.
The distributed parking is a decentralized system — Blockchain.
Wait! We missed something.
All decentralized systems are not Blockchain! Yes, Blockchain is a particular type of decentralized system that has a unique property. Which property? Let’s talk about it.
“Blocks” make Blockchain
Let’s revisit our distributed parking example and make a small change. Assuming the same car parks in the same space each day, and that the lock to a particular space is generated when a car is parked inside it and each decentralized space is numbered in sequential order. The lock-key pair of space #50 is based on the lock-key pair of space #49 and also on the features (like color, weight, engine number etc.) of the car parked inside space #50. This process starts from space #1 and continues to space #200 or even more.
Each space’s lock-key pair depends on the space’s car features and previous space’s lock-key pair.
Therefore, if a thief tries to break into space #49 and modifies any feature of the car, say its color or registration number, the features of car in space #49 will change, which means a new lock-key pair for space #49 will be generated and since lock-key-pair for space #50 depends on lock-key pair of #49, the lock-key pair for #50 will also change. The same goes on successively for all the connected spaces.
Now, let’s make one last assumption that computing a lock-key pair requires lots of computing resources which means if we have to recompute these pairs if a thief modifies any car feature in any space, it will be practically impossible to recompute all the pairs again.
What happens if a lock-key pair is changed?
If you recall, earlier we talked about all space owners abiding by some rules. One of these rules is to check for a valid space. A space is valid if you can authenticate its lock-key pair and if any lock-key pair gets changed, the lock-key pairs of all the following spaces are invalidated because every pair depends on the previous pair. (Process to validate a lock-key pair for a particular space is very fast as compared to generating one).
This dependence of one pair on the previous pair makes it a chain of spaces and in technical world, these spaces are “blocks”, thus getting its name — Blockchain (a chain of blocks).
Blocks in Blockchain are tied to the next block by hashes just like lock-key pairs in our example. If data in one block is modified, hashes1 need to be recalculated for all the following blocks and since calculating the hash is a very resource intensive operation, it gets practically impossible to do that and hence the network rules out the invalidated block. The calculation of hash is called mining and we will talk more about it in Part 2 of this article.
How do the blocks recover from modification?
All the computers on the blockchain network keep a copy of the full blockchain, so if one block or one complete chain at a particular computer or multiple computers is modified, the whole network tries to compare it with their own copies of the full chain.
If majority of the nodes (or computers) on the network find that the modified chain is invalid, the modified chain is replaced with valid chain from other nodes. This makes Blockchain vulnerable to 51% attack. In simpler words, if more than 50% of the nodes on the network are malicious (or say have a modified chain), then the whole network can be compromised.
Part 2 – Concepts of Cryptocurrencies, Mining and Smart Contracts
X-coin: Ethereum, Bitcoin
X-coin, whether it’s Bitcoin, Litecoin, Ether or others, are cryptocurrencies (derived from the word cryptography) – the concept that powers the underlying technology of your favorite coin. Why do we need these digital coins? Apart from sending or receiving money from your friends, these coins are used to incentivize the computers on a Blockchain network. What? Let’s step back and bring back the parking garage example in to the picture.
Pay for Parking Space vs Cryptocurrency
If you remember from Part 1, we mentioned that decentralized space owners will rent their parking spaces to those in need. Now, you might be thinking, how would a lessee pay the lessor? Simple! Through the bank transfer. But why would someone share their bank details with a stranger who is renting their parking space? That’s a valid question.
This problem can be solved by using a digital Wallet, such as PayPal. The space owner uses their PayPal email address to receive payments. This way they don’t have to share their bank details to strangers and, it also offers anonymity. By using an email address to receive payments, the garage owner can stay completely anonymous to the tenant and same goes for the tenants as they will also be paying from their PayPal accounts.
Now, let’s compare this with cryptocurrency. In crypto world, it’s almost the same except with a small difference: instead of using an email address you use a Bitcoin, Ethereum, or other coin wallet address, which is unique to you. You send the coins from your X-coin wallet to the receiver’s X-coin wallet. Since, the network is full of strangers, revealing bank details for money transfer would be a big problem. Therefore, using wallet addresses facilitate the users to send and receive payment by staying anonymous to everyone on the network and this is also one of the reasons why some countries have banned crypto, and why it is very popular in the illegal world.
If you are with me to this point, I am sure you must be thinking that you can transfer money from bank to PayPal but how does that happen in crypto world? Let’s look in to this.
Genesis of the First Coin or New Coins
Just like transferring money from your bank to PayPal, you can transfer money from your bank to your X-coin wallet by buying coins from a registered Exchange. The question here is, how did the first X-coin come into existence, and how are new coins added to the system? Before we answer this question, let’s take a look at another familiar term “mining”.
What is Mining?
If you remember, in Part 1, we talked about computation (process to calculate lock-key pairs) and validation (process to check if a lock-key pair is correct or not). Let’s assume that all the parking space owners participate in the process of calculation of a new lock-key pair, which requires lots of computing power (brain power) and time. So, the rule of this game of computation is whosoever calculates the correct value first, wins! This entire process of computing the correct lock-key pair is termed as “mining”.
But why would a space owner spend time to work on computing a lock-key pair? We need to incentivize them! Let’s assume that the winner gets a cash prize. The prize money is money that wasn’t with the space owners before (or you can say it wasn’t a part of the parking system). It is the fresh or the new money that was introduced to the parking system after mining in the form of prize money. Now, let’s use this analogy to understand mining in a crypto world.
Crypto World Mining
As you now know, all the blocks in blockchain are safeguarded by one-way hash functions (hashes), which are calculated based on previous block’s hash and current block’s data. Thus, binding all the blocks in a chain. This hash computation is resource intensive because it requires you to hit and trial every possible value to get a correct hash (just like what space owners did). So, the more values you can try per second, the faster you will be able to compute the correct hash (This is why you might have seen your friends buying big machines to mine Bitcoin or any other X-coin).
But the same question arises again, why would someone lend their computer to the X-coin network to perform these resource intensive computations? The answer is the same – incentives. Any computer that is able to calculate the correct hash first is awarded with a new X-coin. This new coin wasn’t a part of the system before. This is how the new coins come into the system.
But why the name “mining”?
Well, cryptocurrencies are considered to be digital assets or commodities just like gold or silver, or other metals and minerals. Since, the process of extracting these metals from their mines is known as mining, the cryptocurrencies computations also got the name “mining” because mining brings a new coin to the system.
Now, let’s move out of the cryptocurrency world and dive in to application development on Blockchain.
Decentralized Applications (DApps) & Smart Contracts
Researchers are realizing the benefits of the underlying technology of Bitcoin (which is Blockchain) for different applications apart from just cryptocurrencies. This is where smart contracts can be useful. Before we dig in the technical side, let’s continue with our parking example. For a moment let’s assume that there is no prize money included for mining winners.
To simplify payment at the parking facility, there is a fee-collecting machine outside it which allows you to read a barcode using your phone and make the payment from your PayPal account. This machine collects the money and computing of the lock-key pair (mining) starts. Once that garage’s lock-key pair is generated, the machine sends that money to the garage owner who won the mining contest.
The fee collecting machine in the above scenario is a smart machine because it has determined whom to send the collected money once lock-key pair was generated. And in case anything buggy happens, like a technical error, the machine refunds the money and the process can be repeated, or the car leaves.
Similarly, on Blockchain this smart machine is called a smart contract — a piece of code that does everything for you on blockchain. As all garages have smart machines, all the computers on the Blockchain have a copy of the smart contract. So, when you send money, it makes sure that you have enough money to send and the receiver gets the money and in case of any error, it reverts the transaction.
Smart contracts are not just for money transactions. They can be used to store or modify data on the Blockchain which can be a YouTube-like model for videos, or a Dropbox-type model for
storing files, or even games like Cryptokitties. The list of use cases is endless!
What Happens When there are No New Coins?
Earlier in this article we assumed that there is no prize money to the winners for computing correct hash value. This gives birth to a new question — Why would someone rent out their computers if they will not be rewarded with new coins? Just like the fee-collecting machine outside the parking garage collected money and disbursed the revenues, including the new currency to the winning garage owner, a fraction from every transaction on the Blockchain is collected. When a block on the Blockchain is mined (its hash is computed by all the computers on the network), the computer winning the mining contest, gets the money deducted from all the transactions mined in that particular block (each block contains a fixed number of transactions) as a reward or incentive. This keeps the crypto model sustainable even after no new coins are issued. Now you know why your friends are buying big machines!
Conclusion
Bravo! You finally acquired the basic knowledge about the Blockchain and its components. I hope this two-part article helps to strengthen your foundations in this emerging technology. From here on, if you are a tech person, you can start learning about developing applications on Blockchain or even setting up your own Blockchain.
If you are a non tech person, you can start looking out for problems that can be solved using Blockchain. This will help you deepen your knowledge about the application part of this amazing technology.
Sidharth Malhotra
ML Eng. @Bola | CS Grad. Student | SW Dev. | ML, SaaS
https://sidharthmalhotra.in
1. https://en.wikipedia.org/wiki/Cryptographic_hash_function